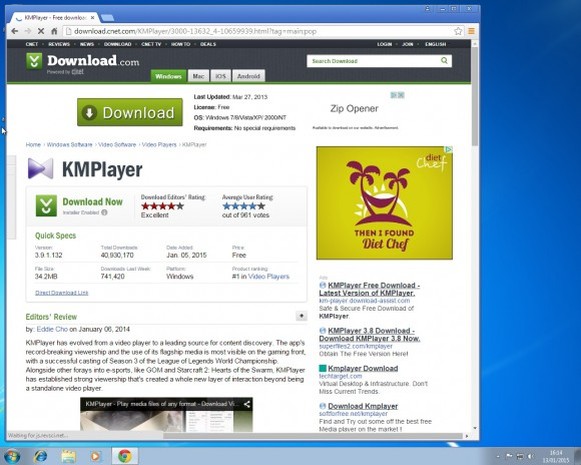
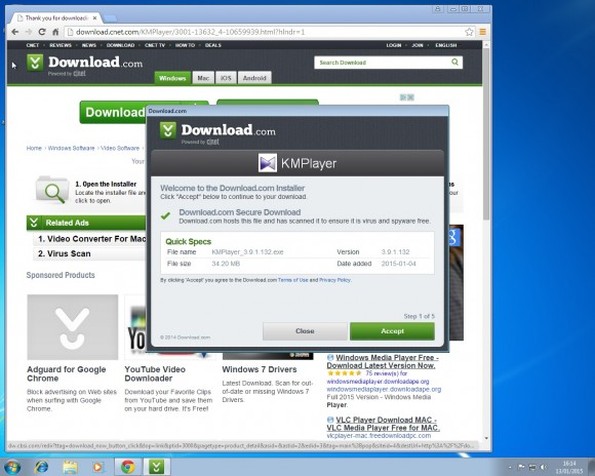
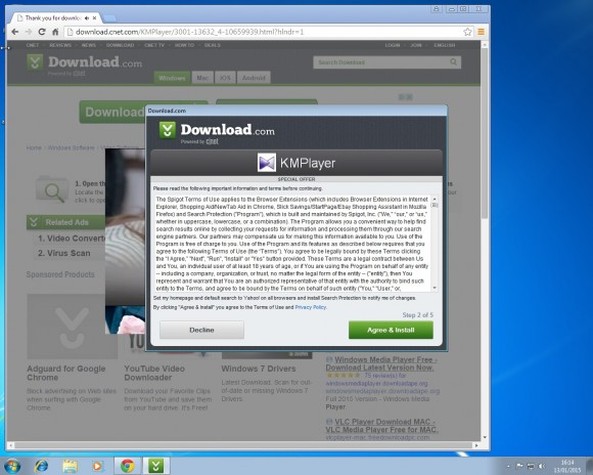
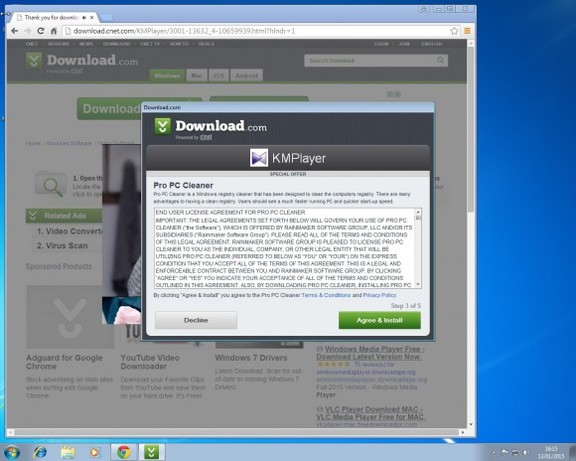
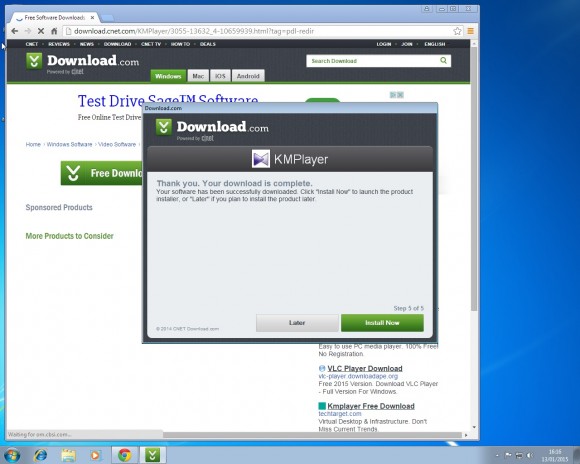
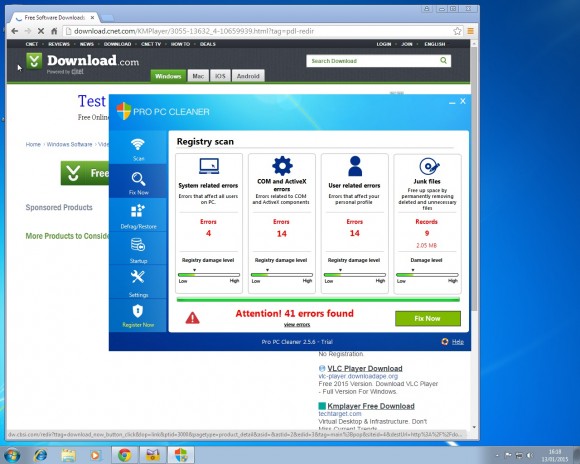
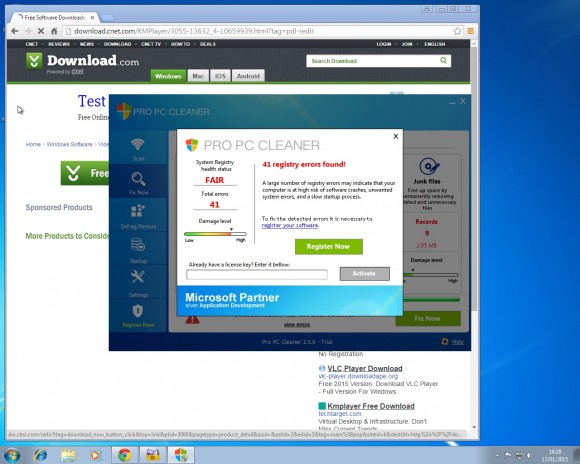
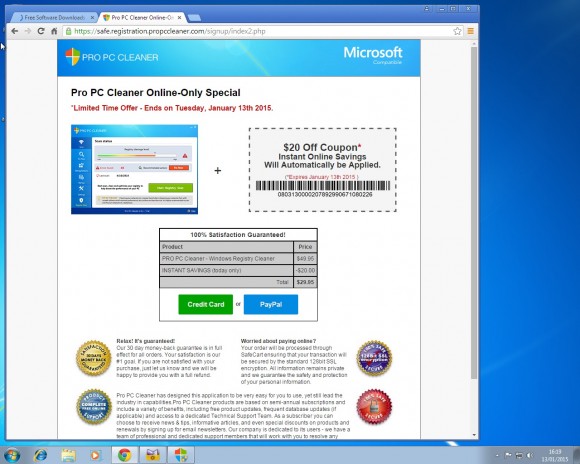
Welcome to PC Tech for Hire, Montgomery Alabama's professional residential and small business computer repair and service provider. Thanks to Cadishead Computers for the use of this series of articles. KMPlayer Following on from part 1 of our series “what happens when you install the top 20 download.com apps” – Avast. We are now onto no 2 on the list KMPlayer. What is KMPlayer? Well according to download.com it has evolved from a video player to a leading source for content discovery. EDITOR: Whatever that means! The applications record breaking viewership and the use of its flagship media is most visible in the gaming front, with a successful casting of Season 3 of the League of Legends World Championship. Alongside other forays into e-sports, like GOM and Starcraft 2….. Blah.. So, how did we do with KMPlayer? First, do you see the ‘Installer Enabled’ Under the download now button?. It’s kinda grey, and it by itself doesn’t appear to be anything obtrusive.. Or so you would think. Part 1. Ok, this is fine, however this is step 1 of 5? Step 2: You are agreeing to the following: The Spigot Terms of Service (which you have agreed to, because you have clicked Agree and Install) Browser Extensions in Internet Explorer. Shopping Aid / New Tab Aid in Google Chrome Slick Savings / Start Page / Ebay Shopping Assistant in Mozilla Firefox. Finally Search Protection! All the above just by clicking agree and install. So irrespective of which internet browser you use, it WILL be affected in some shape or form. Note how the Decline button is greyed out. Making it appear that you can not click on it? So we click Agree and Install on Step 3 of 5. This time, we have agreed to Pro PC Cleaner. Which is supposed to be a Registry Cleaner. More on this later in the series. Finally we get the Installation button for KMPlayer. Bearing in mind, for the previous 4 steps, we have already agreed to and installed 8 assorted programs! Again more on this later in the series. Remember the PC Pro Cleaner which we ‘Agreed to install’ only a couple of minutes ago? Well it suddenly popped up, and found 4 errors in a couple of seconds, which is said required removal. Ummmm.. We continue to let it scan in the background. So now we have agreed, downloaded and installed our previous 8 assorted ‘wanted’ programs, plus the one we DID want, and NOW SEARCH PROTECT comes up, saying it requires installation. Note: it clearly states that Search Protect WILL set your home page AND your default search to TROVI Search for Internet Explorer, Firefox and Chrome. Not only that, it will ALSO prevent third parties from changing ‘my’ Browsers Home Page AND Search Settings. Ermm.. Hang on. Wasn’t this covered previously in the download.com policy settings?. But that’s right.. Because we have ‘ALLOWED’ the browser changes, and ALLOWED the programs to be installed, the policy settings from Download.com, mean squat. Now getting back to the PC Pro Cleaner, which was so conveniently installed for me. This had ‘found’ 41 errors. Nice of it to tell me. Again note, this is a brand new installation of Windows. There are NO errors! So we click on Activate We can get an instant $20 off, if we pay for the program now. So it would only cost me $29.95. Thanks, but I think I will pass. I know that this machine is clear of any and all issues.
See how easy it is for the likes of these programs to remove money from your wallet into their bank?. So until the next installment, PLEASE BE CAREFUL ON WHAT YOU CLICK, AND AGREE TO INSTALL! Next time, we will deal with YTD Video Downloader.
0 Comments
Welcome to PC Tech for Hire, Montgomery Alabama's dependable residential and small business computer repair and service provider. Thanks to Cadishead Computers for the use of this series of articles. Over the next few weeks, we will be writing a series of articles about the top 20 applications which can be downloaded from Download.com. Together with how these said applications install other assorted software behind the scenes.. This would read better as “what’s more YOU, yes You, 9 times out of 10 will allow this to happen!” When you do this, you’re allowing your computer to install assorted malware/spyware/viruses. So read on for what happened to our virtual machine, when we simply allowed each application to install what ever it wanted to. Together with the results of our malware scans afterwards. So, grab yourselves a cup of tea, or coffee, as you may not believe what happens... We installed the top 20 apps from Download.com, and you may not believe what happened to our virtual machine! Well… You may have a good guess, if you have already done something like install a free piece of software. Bad, bad things are what happens. It’s going to be a good series..Join us for the fun! For the purpose of this experiment, we have just clicked through all the regular installation screens with default options. i.e. we have NOT watched what we are downloading. This was done on a new install of Windows 7 on our virtual machine. We have installed the top 20 applications. You could be asking, why choose Download.com?. The reason is because their policies page clearly state that they DO NOT allow any nasty/bad/ virus infected software on their site. What’s more is that they do NOT accept any software which should have any of the following included inside it. Download.com does not allow malicious software on the site. We test all submitted software products according to comprehensive criteria. Viruses, spyware, and malicious software. We do not list software that contains viruses, Trojan horses, malicious adware, spyware, or other potentially harmful components. We do not list products known to contain such items in instances outside Download.com, and we may disallow products from publishers that we feel violate the spirit of this policy. We do not accept the following types of software: Software that installs viruses, Trojan horses, malicious adware, spyware, or other malicious software at any point during or after installation. Software that installs the above items via links to other software or Web sites.Links on publishers’ Web sites that may enable the installation of the above items. Software that installs without notice and without the user’s consent. Software that includes or uses surreptitious data collection. Software that collects and transmits information about end users or end users’ computer usage without adequate prior notification. Software that diverts or modifies end users’ default browsers, search-engine home pages, providers, security, or privacy-protection settings without the users’ permission. Software that interferes with users’ control and privacy. Well, with all of the above supposed protection in place from the very website itself, one that is supposed to be trustworthy, why should you worry? However, please note where it states ‘without the user’s consent’. What this actually means is, IF YOU DO NOT CLICK NO OR DENY, then it WILL install the other assorted software. So BE WARNED!. SERIOUSLY DANGEROUS!. DO NOT TRY THIS AT HOME! If you do attempt this at home, then DO NOT be surprised when your computer wants you to put it back into the box it came from, and return it from whence you bought it. Either that, or take it to a professional to clean up everything that you have done.. In fact, if you have already installed any of the software we are going to mention here, it would be a good idea to have your machine looked at by a professional!. We have mentioned previously against why you should not use supposed ‘System Tune Up’, or ‘Registry Cleaner’ programs. So where do we start off. We fired up our virtual machine, and went directly over to download.com. The first thing we did was to go to the windows downloads page, and see what we could download from the 20 most popular downloads. This list may change at a moment’s notice, but this is as it stands today. 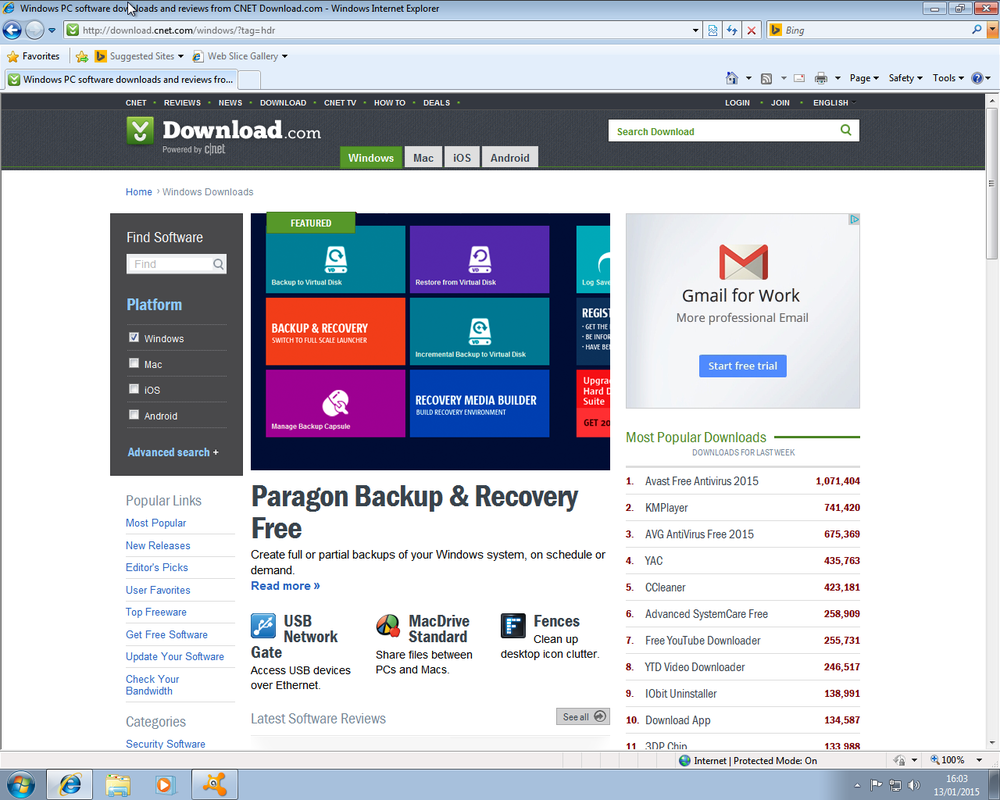 The list of the current top 20 programs are Avast Anti virus – Protect your PC and data from hackers and thieves. KM Player – Play digital media of various formats including incomplete, partially downloaded, or locked files. AVG Anti virus 2015 – Protect your computer from viruses and malicious programs. YAC – Protect your PC from browser hijacker, malicious plug-ins, malwares, adware, various viruses. CCleaner – Clean up junk files and invalid Registry entries. Advanced System Care – Speed up a slow PC, shorten startup time, and protect online privacy. Free You Tube Downloader – Download YouTube videos and convert to multiple formats. YTD Downloader (You Tube Downloader) – Download and convert videos from video streaming sites. IObit Uninstaller -Remove unwanted apps, browser plug-ins/toolbars and Windows 8 pre-installed apps thoroughly. Download App – Keep the software on your Windows computer up-to-date and running smooth. 3DP Chip – Download the latest device drivers with few clicks GOM Media Player – Play video files of multiple video formats. Virtual DJ8 – Mix digital music or video replacing your turntables and CD players. Malwarebytes Anti Malware – Detect and quickly remove malicious threats to your computer. Photoscape – View, edit, print, or add frames to your photos. Start Menu 8 – Bring back “Start” menu for Windows 8/8.1 and advanced start menu for Windows XP/Vista/7 and 10. Driver Booster 2 – Update drivers from online database in one simple click. Internet Download Manager – Increase your connection speed and recover broken downloads. VLC Player – Play audio and video files in real-time and streaming modes. Ad-Aware Anti virus – Protect your personal computer against virus and spyware attacks. This list is good to know what NOT to download. The plan is to download and install the top 20 programs. Although as you can see in the list above, within the top 3 programs, 2 are anti virus programs and the last one is Ad-Aware Anti virus. Since we only want one, and we detest AVG with a passion, and have never used Ad-aware AV, we are just going to install Avast. Surely one of the top rated (in terms of downloads) will stop our machine from being infected with a virus etc? Therefore for the testing purposes of this series, we will only be downloading and installing 17 of the above programs. Results may differ from our testing to yours in a real life scenario. Please bear in mind this is a fresh windows install. With nothing else installed at the time. No windows updates, no programs what so ever! 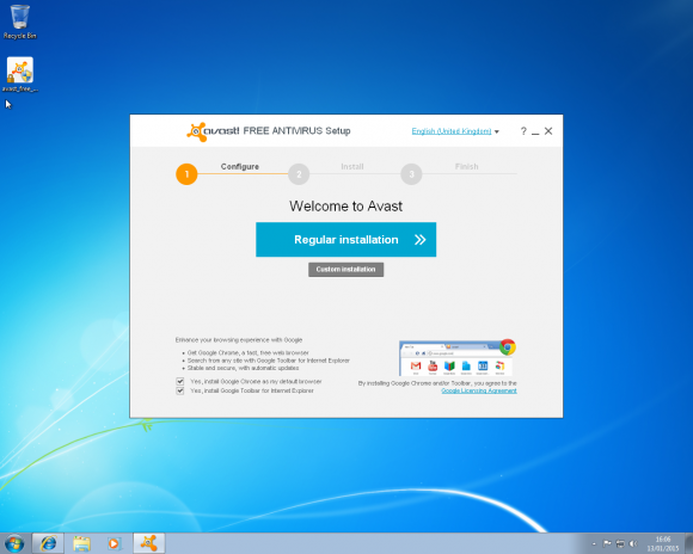 Avast Anti Virus. Bundled software is the same as in-app purchases made on a mobile phone. Here to stay, unless you say no! Well this time, it is not spyware/bloatware/malware being installed, as well as Avast. Google Chrome is a fantastic browser, and one of our favoured ones. However the bundling of software starts right here. The free software vendors make more money by allowing bundled software to be installed with their installations than they do by selling their own software. This is our own personal view. This time, at least, Avast is bundling something good, but it still breaks Download.com’s policies wouldn't you say? Our next installment will be KM Player. Thanks again to Cadishead Computers for the use of this series of articles. I hope you'll benefit from the information that will be given throughout the series. This will definitely be a learning experience! Hopefully you'll learn what NOT to do when downloading and installing programs. But, if you get in a bind, I'm always here to help! Click on my Contact Page to send me a message and I'll get with you as soon as possible. Welcome to PC Tech for Hire, Montgomery Alabama's affordable residential and small business computer repair and service provider. The world of computing can be a confusing place. PC Tech for Hire has put together a simple jargon buster to help you understand some basic aspects of the world of computing.
Anti-virus: Anti-virus software provides you with extra security from computer viruses. Broadband: Broadband is a method of connecting to the internet. Broadband enables large amounts of data to be transferred at faster speeds than dial-up. Browser: A browser is a computer program that enables you to read and view websites over the Internet. Computer Programs: Computer programs contain a set of instructions for your computer to follow. A computer program does not run its instructions unless executed by the CPU. CPU: The CPU or processor, is the brains behind your computer. The CPU is responsible for executing your computer programs. Dial-up: Dial-up is a way to connect to the Internet using a telephone line and a modem. Email: Email is the exchange of electronic mail between users around the world. Firewall: Firewalls provide extra security which protects your computer from unauthorised access by crackers. Graphics Card: A Graphics Card, also known as a video card, is a component which generates and outputs images to a display. Hacker: Hackers are people who enjoy exploring and learning about computer systems. They are often confused with crackers, who often break into computer systems to steal information and cause as much trouble as possible. Hard Drive: The Hard Drive stores your data on your computer. Unlike RAM memory, when power is lost, the data remains intact. Hyperlink: A piece of text or image, that when clicked takes you another web page. Internet: The Internet is a network of networks around the world. The Internet is responsible for data communication. IP address: An IP address is a unique numerical number assigned to devices connected to a network. Memory: The main type of memory inside your computer is RAM. Ram (random access memory) stores data temporarily in your computer. When the computer is switched off, the data is lost/erased from the RAM. Modem: A modem is a device that allows computers to send and receive data over telephone lines. Motherboard: The motherboard is a circuit board, which provides a way for your devices to communicate with each other. Network: A Network is when two or more computers are connected together to share resources and information. Router: A router is a device that allows two or more networks to be connected together so data can be transferred between them. Server: Is a powerful computer system on a network that stores data and also responsible for resource management. Sound Card: A Sound Card is a component which generates and outputs audio/sound to a set of speakers Switch: A device that networks two or more computers together. URL: URL (Uniform Resource Locator) is a way to locate a file/website over the Internet. For instance, the URL for SJH Computing is http://www.sjhcomputing.co.uk USB: USB (Universal Serial Bus) is a way to connect different devices, such as digital cameras to your computer. Virus: A computer virus is a program that is designed to cause damage to your computer. Web page: Is a document hosted on the Internet, which when combined with other web pages creates a web site. World Wide Web: The World Wide Web is a collection of interlinked hypertext documents which is accessed via the Internet. Have any questions you would like answered on my blog? Contact me here with your question, and you will see a response in a future blog post. Welcome to PC Tech for Hire, Montgomery Alabama's trusted residential and small business computer repair and service provider. When it comes to anti virus & spyware programs, just how much difference is there between the paid for versions and the free ones?
In the “olden days” when computer viruses were just beginning to hit their heyday, you had to pay for all virus protection software. Nowadays, there are plenty of free virus protection programs available for users to download from the Internet. There are also many paid programs available, so you may be wondering whether you need to pay for virus protection software or if the free programs are adequate. To answer that question, you need to determine what your virus protection needs are and in what capacity you will be using your virus protection program. For example, the majority of free programs are designed for personal home use only, not for business use. So if you’re looking for virus software for your business, you’ll have to purchase a licensed version. There are several other differences between the paid and free versions as well. Performance The main reason you install virus protection software is to protect your computer against viruses, which can harm your computer. Tests have shown that both the free and the paid virus protection programs perform comparably in terms of detecting viruses on a computer. While this is incredibly important, there are other types of malicious programs and components that can infect your computer and cause irreparable damage or steal personal information. Detection and removal of spyware, malware and other nasty items is where the paid programs shine. Most of the free programs also detect malware, but the paid programs do a better job and detect more of the little nuisances, which means your computer is cleaner and your information is safer if you’re using a paid program. Additional Features Another way paid virus protection wins over users is by offering additional features. When comparing virus protection programs, you should take a look at these added features and see if any of them appeal to you. Examples of added features include parental controls, enhanced spam filters and identity theft protection. Avast’s paid program, Internet Security 6 Package, even opens up a new desktop for sensitive information, such as online banking, so other programs cannot steal account numbers or passwords. Support One of the major differences between free and paid virus programs is the customer support. Support is typically lacking or nonexistent with free programs because there is no money being exchanged. You may find a FAQ section on the company’s Web site or a limited help section built into the program, but the companies offering free software typically do not invest much money in support for these free programs. Paid programs, on the other hand, typically offer online and phone support for users. While you may not consider support to be a big deal, keep in mind that the free programs are often a bit more difficult to operate and navigate. If you decide on a free program, but are unable to set it up properly, it is useless. If you’re still unsure of whether to go with free or paid virus protection, think about how you use the Internet. For users who are frequently downloading files and surfing a wide range of sites, a higher level of protection is warranted. For people who do minimal surfing, do not download many files and do not use credit cards online or engage in online banking, a free version is most likely fine. You could always see if the paid program you like has a free trial and compare it to a free program for yourself. That way you’ll know if it’s worth spending the money each year for the paid version. Good luck, and stay clean from those malicious viruses! For a quality paid service, look no further than my ProActive Care - Antivirus service. Not only do you get the benefits listed above for a paid service, you get the added bonus of having someone actually monitor the service. I will keep an eye on virus scans to make sure viruses or other malware is being detected and removed correctly. And in most cases, my service costs less than other paid solutions. Contact me for a free trial! What is "Ransomware"?Welcome to PC Tech for Hire, Montgomery Alabama's dedicated residential and small business computer repair and service provider. Ransomware is a type of computer virus that "holds" your computer hostage. These type of viruses can prevent you from using the internet, your computer, specific programs, or in some cases, encrypt your data. One thing these viruses all have in common is that they want you to pay them in order to release your computer from their grasp. While some keep their word, and once you pay they delete themselves, not all of them do and they simply take your money and ask for more. Common payment methods include Moneypak, Paypal, wire transfers, etc. I'm only going to outline the more common of these, what they look like, and what they are going to do.  The FBI virus is the more common one for those in the United States. There are many versions of this one, some claiming to be Interpol or another local police agency to your country or region. One thing that really makes this trojan virus stand out is that it pops up your screen on says your computer has been used for illegal activities such as pirated software or child pornography, and your actions on the computer are being monitored by law enforcement. The warning informs you that in order for you to have your computer unlocked, and the charges dropped, you must pay a fine using an anonymous prepaid cash service. This virus will give the illusion that this is real, but this is not how law enforcement works. If they knew where you were, and what you did, they'd knock on your door, not lock your computer. While many antivirus programs do in fact prevent or even remove this virus, this virus is not always traveling alone. One of the things this virus does is send a few of its friends in first. These friends will disable your computers security, or stall it, so the virus can get in there and take control of the computer. So how do you get this virus? Typically it is done through downloading what appears to be legitimate software from websites, especially torrent downloads. The less common way is through drive-by means, or visiting a website that has been infected to download the virus without your knowledge in the background. In some cases, this virus can be removed remotely, but in most cases the computer has to be cleaned of this virus either on site or in a shop. It is strongly encouraged to have the FBI virus removed by a professional as this virus can return after a computer has been restarted if it has not been removed completely or correctly. To really prevent yourself from getting infected, make sure you only download software from a legitimate website, and never download unverified torrents or pirated software. CryptoLocker came out in mid to late 2013. This is a computer worm virus, or one that spreads through your network. The mission of this virus is to encrypt your files and hold them for ransom. Typical infections are via attachments in malicious emails, and most recently through drive-by downloads. Once the CryptoLocker downloads on to your computer, it generates a 2048-bit RSA encryption key, and uploads it to it's server. Once the key has been generated, it begins encrypting data on any local or network storage device that your computer can access, targeting files matching a specific whitelist of file extensions. The virus will inform you of its presence, and include a count-down (typically 3 to 4 days). Once the countdown has hit 0, everything the virus was able to encrypt has been encrypted, and the encryption key deleted, making recovery impossible. CryptoLocker will demand a payment, we've seen as low as $200 and as high as $600, in order for your files to be encrypted, but the decryption process must start before the countdown hits 0. Any files that have been encrypted can not just be decrypted, a 2048-bit encryption key would take thousands of years to discover. But do not fear, there are many things that can be done to safeguard your computer, and recover lost files. Protection Make sure you perform regular backups of your computer. Whether it is ProActive Care - Backup or any other means. If you use an external hard drive, remember to unplug it and store it somewhere safe to keep this drive being encrypted as well. Install CryptoPrevent or call us to install it for you. Once Infected The number one thing you should do once you discover your computer is infected is turn it off. The virus can not encrypt files if the computer has been turned off. Some claim that unplugging it from the internet will stop it from encrypting, this is not true. Next, do not pay the ransom. The biggest reason is because you would be feeding a criminal and recovery can be less than what the cybercriminals are asking for. Give us a call immediately to have your computer recovered from this virus. We will have to take your computer, and turn around times for recovery do vary. Make sure to give us all the backups you have, or access to your online storage backup. Other Ransomware Viruses Windows Product Activiation is another worm virus that is not as famous as the other two, but it gets the job done as far as what it does. If you've already activiated your Windows installation, you should not have to do this again unless you replaced a major hardware component inside the computer itself. Always consult us before you write this off as a virus. This virus informs the user that you have to re-activate your copy of Windows due to being a victim of fraud. There will be a pop-up trying to take you to a website (a link that normally does not work), and instead has you call one of various international phone numbers to input a 6-digit code. While the claim is that the call would be 100% free, the call is actually routed through a country with an extremely high international phone rate, and then they place you on hold for a long while. This causes the user to incur a very large long distance charge. If you believe your computer to be infected with ransomware, or any other type of malware, please contact us for a Virus Removal service. Ask about my ProActive Care - Antivirus service that can help prevent a lot of these types of ransomware and malware. Laptop Buying GuideWelcome to PC Tech for Hire, Montgomery Alabama's premier residential and small business computer repair and service provider. This is the time of the year when people are looking for that perfect gift. And what could be more perfect than a new laptop!? I'm often asked what laptop they should buy, which one is the best, etc. All models of computers/laptops will end up having a problem at some point. My opinion? Follow these simple rules and you just bought the best laptop! 1. Figure out a budget. Remember that with a new computer, you may need to buy new software. And for those that want help setting it up, I quote 2-3 hours to get everything installed and configured. 2. Make sure you buy a laptop in person. Buying online gives you no sense of how the computer feels, weighs or views in bad/good/extra light. If you buy online, be sure to buy from a reputable company that you know you can return items too easily. 3. If you go to a store, here are some tips!
A good work laptop is approximately $500-$900. You will pay more for higher quality (SONY) and of course for a faster processor, solid state hard drive and more options (longer battery life, docking station, etc.) Many folks also ask about the processors and hard drive space, etc…my answer is you’ll be ok probably if you can find a computer that fits your needs with the list above. Those are much more important. Most computers today come with plenty of hard drive space. Don't forget to include my ProActive Care services with the purchase! Help your new purchase last longer with ProActive Care - Antivirus, and keep backups of all your data withProActive Care - Backup!  Welcome to PC Tech for Hire, Montgomery Alabama's professional residential and small business computer repair and service provider. In the famous words of Joni Mitchell, you don't know what you've got until it's gone. Unfortunately for many home computer customers, not having a reliable data backup solution is a painful lesson to learn. As we all become increasingly dependent on our digital files, having a copy, or multiple copies, of those files is a crucial element of keeping your data safe. The data on your computer or mobile device can disappear in an instant - succumbing to accidental deletion, corruption, malware encryption or theft. The best way to prepare for a data disaster event is to make sure that you have a workable, reliable and verifiable backup solution in place. A Workable Backup Solution The first thing that you need to do when considering backing up your data is to find a solution which works for you. People use their computing devices differently, and therefore a backup solution should work with your computing experience. Are you the type of person who prefers to control exactly when you backup your data or would you rather "set it and forget it"? Do you prefer having your data close by, say on an external hard drive, or would you rather have it available 24x7 via the Internet? Does your data reside on just one computer or on multiple devices? Answers to these questions will help you decide on the best backup solution for your situation.  4 Key Elements that Every Backup Scheme Should Have Your backup needs to be automatic. Life is too busy for most of us to consistently remember to start backing up our data. Most backup software and services, though, can be scheduled to start automatically. Some programs even backup instantly every time a file is added or changed. Don't let it be your job to remember to plug in a storage device or to kick off a backup routine. Let your chosen solution take care of that work for you. Your backup should be verifiable. Many people have a backup plan in place, but unfortunately not many have a restore plan in place. If you are not sure whether or not you can successfully recover the files that you have supposedly backed up, then you don't have a backup plan! Part of your backup routine needs to be periodic testing to make sure your backups are valid. This may be doing something as simple as restoring one of your files or folders to an alternate location on your computer. If you can regularly successfully restore files from your backup when you don't necessarily need them, then chances are better that you will be able to restore them when you do need them. Your backup should Include versioning. It may not be enough to have just one copy of each of your files. As many who have been hit by the Cryptolocker infection have discovered, backup solutions which don't keep multiple copies of files as they are changed are susceptible to being overwritten by malware. Therefore, it is important that your backup solution allows you to restore copies of your files from various points in time in the past. Your backup should be secure. Do you keep thousands of dollars under your mattress because you feel it's more secure than keeping your money in a bank? Many people follow a similar strategy when it comes to protecting their data. Don't assume that your data is secure just because you have a copy of it on an external hard drive attached to your computer. Hard drives can fail at any moment, can be stolen or can fall victim to a virus or a power surge. However, cloud-based backup solutions are, for the most part, much more secure than onsite backups. Most offsite backup solution providers keep their customers' data in tier 1 data facilities with multiple levels of security controls, encryption, environmental protection and co-location. It is safe to say that your data is better protected in one of these "data banks" than under the proverbial mattress in your home.  Backup Solutions that We Recommend PC Tech for Hire has two different backup solutions that we recommend. We offer two solutions because each of them is able to cater to the different backup needs of our customers. The first solution that we offer is Backblaze. This backup company has been in the business longer than most of the others, and it has a reputation for simple, affordable backup services for residential customers. Backblaze's user interface is very easy to understand, and customers are able to determine whether or not their data is secure just by looking at the file names on their computers. Backblaze offers unlimited backup for your home computer for just $50.00 per year, or for $5.00 per month. The second backup solution that we offer is a solution which offers local backup, versioning and fully encrypted backups locally and in the cloud. While the cost per gigabyte is more than Backblaze, my ProActive Care - Backup service allows you to protect multiple computers under the same plan. Therefore, if you are a household with 1-5 computers, this backup solution would probably work better for you and would be cheaper in the long run than Backblaze. Furthermore, ProActive Care - Backup is monitored regularly. That is, we will take on the responsibility of making sure that your devices are being backed up and that your data is able to be restored when needed. The cost for ProActive Care - Backup is $9.00 a month for 10gb of data, and $99.00 for an annual subscription. Larger blocks of data are available if 10gb is not enough. Contact PC Tech for Hire for a custom quote. Both of these backup solutions provide automatic, scheduled backups to a secured data center, easy restoration procedures, versioning and 24x7 access to your files from anywhere via the internet. Making sure that your data is backed up securely is not a difficult task in today's world. However, it does take a bit of planning and initiative on the front end. However, when a data disaster strikes, you will be glad and grateful that you have a solution in place. Welcome to PC Tech for Hire, Montgomery Alabama's dependable residential and small business computer repair and service provider. Be aware of online scams! Tis the season, they say, but what they don’t say is it’s also the season to be scammed. Holiday shopping time is the perfect time for unscrupulous people to exploit peoples holiday cheer to gain access to accounts, steal identities and do other things that should earn them a lump of coal in their stocking. So what do you do to protect yourself? What types of scams should you be on the lookout for? “Your Order Has Shipped/Problem With Your Order/Confirm Your Order” This one’s a popular one because it takes advantage of people not wanting to “mess up” a holiday gift. This e-mail may look like it comes from a popular merchant (Amazon, Walmart, etc) or may be one you've never heard of, and will ask you to confirm or view an order. Once you click the link you are brought to a website which may look legitimate, but is actually designed to steal your login information or collect credit card information. How do you protect yourself? Simple: If you think it’s legitimate, log in to the website by typing the merchants website in to the browser manually – not clicking on the link. If there is an order there, you’ll see it where you normally see your orders (usually under My Account or Orders).  “A Gift Is Waiting For You/Free Holiday Offer” This one exploits the warm feeling you get when you receive a gift, and as we all know, everyone enjoys getting gifts. If a person sends you an e Gift or virtual gift card you may get an e-mail with a link to claim it. You may also get an e-mail claiming to be a free holiday gift for being a valued customer or long time member of an organization. How do you protect yourself? This one is a bit harder to protect yourself from, but it’s a good idea to mention the gift to the person who allegedly sent it. If the gift was from a friend, call or text them and say “I just got an e-mail with an iTunes gift card from you, is this really from you?.” You can also hover your mouse over the link and verify the address goes to the merchant’s known domain name (Apple gift cards should go to Apple.com, Amazon to amazon.com, if one goes to amazon.somenamehere.com, then that’s not really Amazon.) For merchant gifts, call or e-mail the merchant to verify that the offer is real.  “This Price Is Too Good To Be True/90% Off Sale Going On Now” This scam exploits our greed and most people’s enjoyment of getting an amazing deal on something. You will see an offer for a 47" LED TV that usually sells for $800 for $200, or a high end digital SLR camera that normally sells for $500 for$150. You may also see e-mails claiming an amazingly high discount off listed prices on a website that’s given back by mail later or returned to you 30 days after purchase. How do you protect yourself? If a deal is “too good to be true”, it probably isn’t true. If a merchant has a limited loss leader for a retail store or a website (where they sell an item at cost), then that’s possibly true, but expect a very limited number and needing to be the first few online to get one. If an item is sold so far below every other vendor – even below the reasonable cost to make the item – something is probably up. The best way to protect yourself here is to be suspicious and only go for “amazing deals” from trusted vendors you know and have already done business with. A good bit of common sense and reasonable suspicion will protect you when shopping this holiday season, but don’t let these few bad apples spoil your fun. Another way to protect yourself is with my ProActive Care - Antivirus service. My Antivirus/Antimalware service monitors your Internet browsing activity and warns you when you are about to enter a site that is either questionable or is a known malware site. The suggestions I give above should always be followed, however, my ProActive Care service will give you that extra layer of protection. You may be going to malware sites and not even realizing it. Contact me today for a free trial!
 Welcome to PC Tech for Hire, Montgomery Alabama's affordable residential and small business computer repair and service provider. Looking for gift ideas for that special loved one in your life? If you're like me, as our parents and grand-parents age, they seem to have everything they need and it is hard to find a gift for them. What better gift than the peace of mind they will get knowing that their computer is going to stay up and running. ProActive Care Services by PC Tech for Hire is a good place to start for trustworthy, friendly computer service. Starting tonight at midnight, you can sign up for all ProActive Care Services at the once in a lifetime discount of 25%! Click here for more details.  Welcome to PC Tech for Hire, Montgomery Alabama's trusted residential and small business computer repair and service provider. Before getting to the topic, I want to encourage you to visit my blog next Thursday, the 27th of November, for a special announcement! All About Net Neutrality You've probably heard about something called net neutrality in the news. It sounds about as exciting as dry toast, right? But it’s an important concept and I’d like to explain why. This won’t take long, promise! (If you’re more of a visual person, here’s a quick two-minute video explaining it all: https://www.youtube.com/watch?v=L11kLmWha6o ) So what IS “net neutrality”? According to Wikipedia, “Net neutrality (also network neutrality or Internet neutrality) is the principle that Internet service providers and governments should treat all data on the Internet equally, not discriminating or charging differently by user, content, site, platform, application, type of attached equipment, and modes of communication.” Sounds pretty good, right? This is, more or less, the system the internet functions on right now. However, in May of this year, the Federal Communications Commission proposed rules that could change all that. Under the new rules, telecom giants like Comcast, Charter, AT&T and others could create a tiered-internet system--pay to play, if you will--where they get to pick and choose what you get access to for a price. Consider how your satellite or cable TV service works right now. Charter offers several packages to choose from, starting with the most basic tier. The basic one gets you a few basic channels (and a bunch of other ones nobody really wants) for cheap. Pay more and you get more channels. If there’s just one channel you want but it’s in a tier above what you have, you have to pay for that whole other level just for that one channel, like it or not. Or you may not be able to get that channel at all. Maybe your provider doesn't carry BBC America for whatever reason. You’re out of luck! So far the internet doesn't work like this. You can go to any site you like and your Internet Service Provider doesn't choose how fast you can get there, other than the limitations of your modem and copper/cable lines. “Net neutrality creates an even playing field among content providers — both large and small — to the web. And it's great for consumers because they can access everything they want online for no extra charge. Right now, consumers control what they see online — not Internet access providers — and that's thanks in large part to net neutrality,” says Business Insider. But again, all that could change if corporations like Comcast get their way. “Without net neutrality, the company that you pay for internet access could charge you more to visit certain web sites, or could block some sites altogether. Or they could also just slow some web sites down: for example the Comcast video site might work very well, while YouTube would be slow, etc.” says Business Insider. If you don’t think this is a good idea, you’re not alone. Here are ways you can take action: http://www.savetheinternet.com/blog/2014/05/16/net-neutrality-so-now-what |
Ronnie MorganHi! I'm Ronnie, your PC Tech for Hire for the Montgomery, AL area! Let me know if you need my 25+ years of experience to help you with your computer needs. Archives
January 2018
Categories
All
|


 RSS Feed
RSS Feed